New security alert of very high severity (CVSS Base score 8.8), concerning the Samba server.
A flaw in its system could enable an attacker to bypass the security restrictions (CVE-2023-4091) and (CVE-2023-4091).
Samba is a server that uses TCP/IP on IBM i to interact with Microsoft® Windows® clients or servers as if it were a Windows file and print server.
The flaw reveals that a remotely authenticated attacker could bypass security restrictions, caused by a flaw when using the acl_xattr module:
Samba VFS with the smb.conf parameter “acl_xattr:ignore system acls = yes”.
By sending a specially crafted request, an attacker can exploit this vulnerability to truncate 0-byte files.
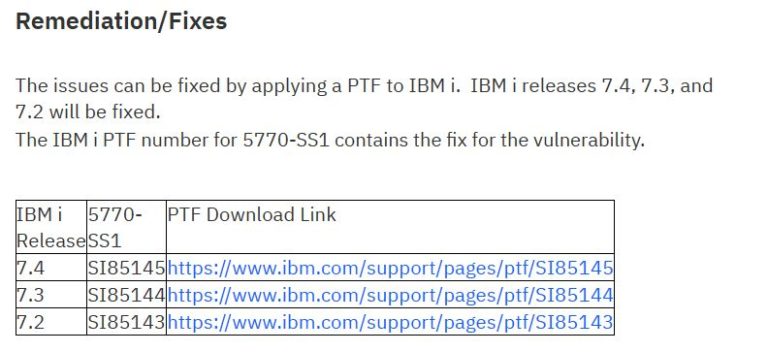
IBM i has corrected the vulnerability in the Samba implementation by providing a patch as described in the remediation/corrections section or on the site (https://www.ibm.com/support/pages/security-bulletin-ibm-i-vulnerable-due-flaw-samba-which-could-allow-attacker-bypass-security-restrictions-cve-2023-4091) and we strongly recommend that you apply the patch that corresponds to the version of your machine:
Posted in Alert