Hello everyone!
👉 This post is the second part of our security bulletin on OpenSSL, following on from our first part on Node.js (📎 link to first part here). Today, we focus on vulnerabilities discovered in the OpenSSL library, widely used for SSL and TLS connection management.
🔍 Summary of vulnerabilities
OpenSSL is affected by 4 denial-of-service (DoS) vulnerabilities. Find out more about each of these vulnerabilities below:
🚨 CVE-2023-6237 – Denial of service via EVP_PKEY_public_check() function
🔹 Impact: Poor management of RSA public keys can lead to excessive delays and a denial of service.
🔹 Exploitation: A remote attacker can convince a victim to use a specially crafted RSA public key.
🔹 CVSS score: 3.1
🚨 CVE-2024-0727 – Denial of service via incorrect validation of entries in PKCS12 files
🔹 Impact: Poor validation of PKCS12 files leading to application crashes.
🔹 Exploitation: A remote attacker can trick a victim into opening a malicious PKCS12 file.
🔹 CVSS score: 3.1
🚨 CVE-2023-5678 – Denial of service when using DH_generate_key()
🔹 Impact: A flaw in the DH X9.42 key generation function can lead to a denial of service.
🔹 Exploitation: A remote attacker sends a request specifically designed to exploit this vulnerability.
🔹 CVSS score: 3.7
🚨 CVE-2023-6129 – Denial of service via a flaw in MAC POLY1305
🔹 Impact: A problem in the MAC POLY1305 implementation can cause a denial of service.
🔹 Exploitation: A remote attacker can send a request specifically designed to provoke the vulnerability.
🔹 CVSS score: 5.9
🛠️ How to correct these flaws?
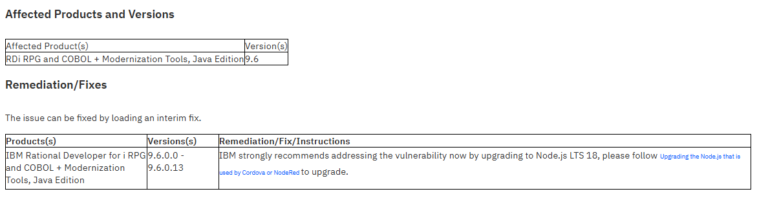
✔️ Update OpenSSL and Node.js to resolve these vulnerabilities and apply the patches. (See Remediation/Fixes for details of specific updates).
📌 Reminder: You can view the full details of these vulnerabilities on the official IBM support site here : 🔗 OpenSSL vulnerabilities details
⚡ Act now to secure your IT environment with STR-iCT!
🔐 Keep up to date with the latest cybersecurity alerts! 🚀