IBM recently published a major security bulletin concerning Node.js and the OpenSSL library. In this first part, we’ll focus on the vulnerabilities related to Node.js, while a second part will cover those concerning OpenSSL.
🛠️ Node.js on IBM i : Main vulnerabilities
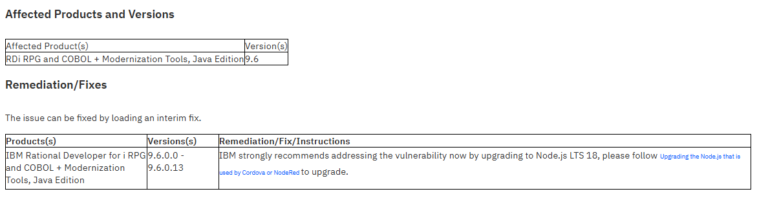
On IBM i, Node.js is mainly used as runtime & SDK for Apache Cordova applications in the RDI (RPG, COBOL + Modernization Tools, Java Edition). Here are the 5 critical vulnerabilities to be aware of:
1️⃣ Leakage of sensitive information: Node.js allows a remote attacker to exploit a vulnerability in the cryptographic library’sprivateDecrypt() API. An attacker can perform a hidden synchronization side-channel during error handling, which would allow sensitive information to be obtained.
CVSS score: 5.3.
2️⃣ HTTP request contraband: Thanks tocontent length obfuscation, an attacker can send specially designed request headers to poison the web cache, bypass firewall protection and carry out XSS attacks.
CVSS score: 5.9.
3️⃣ Denial of service: A vulnerability allows an attacker to exploit a read error in unprocessed HTTP requests with an unrestricted trunk extension. This can lead to system resource exhaustion.
CVSS score: 7.5.
4️⃣ HTTP/2 assertion failure: By sending a small quantity of malformed HTTP/2 packets, an attacker can cause the HTTP/2 server to crash.
CVSS score: 7.5.
5️⃣ Elevated privileges for local attackers: An authenticated local attacker can exploit a problem in the implementation of the CAP_NET_BIND_SERVICE exception to inject code with elevated privileges, thus compromising the system.
CVSS score: 7.8.
🔧 Remediation: How to correct these faults?
To correct these flaws, simply update your version of Node.js. See Remediation/Fixes for details of how to apply the patches.
📑 Full details and security updates
Find all the vulnerabilities and their solutions on the official IBM support site: Link to IBM support
⚡ Agissez maintenant pour sécuriser votre environnement IT avec STR-iCT
🔐 Keep up to date with the latest cybersecurity alerts! 🚀